
Understanding of insider threat far from complete: U.S. report
August 9, 2017 by Canadian Underwriter
Print this page Share
Almost half of respondents to a recent U.S. survey are unaware of the potential for financial losses associated with an insider incident and a third do not know how much related losses are costing their organizations.
 Findings indicate many organizations do not realize insider-related attacks can cause serious damage, notes a statement Monday from Dtex Systems, which provides user behaviour intelligence and insider threat detection services.
Findings indicate many organizations do not realize insider-related attacks can cause serious damage, notes a statement Monday from Dtex Systems, which provides user behaviour intelligence and insider threat detection services.
In all, 45% of respondents to the survey – details of which are included in a SANS report, sponsored by Dtex, Haystax Technology and Rapid7 – say they do not know the potential for financial losses associated with an insider incident.
In addition, 33% report they do not know how much related losses are costing their organizations, notes the report, Defending Against the Wrong Enemy: 2017 SANS Insider Threat Survey.
Beyond the costs – Ponemon recently reported organizations were spending upwards of US$4.3 million to mitigate, address and resolve insider-related incidents – is the worrisome finding that just 18% of respondents note they have a formal incident response plan with specific provisions for insider threats.
Additionally, notes the Dtex statement, only 38% of those with response plans admit their detection and prevention capabilities are ineffective.
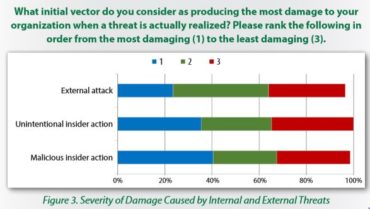
“The critical element is not the source of a threat, but its potential for damage,” emphasizes the report. “Evaluating threats from that perspective, it becomes obvious that although most attacks might come from outside the organization, the most serious damage is done with help from the inside.”
The report points out that sources of insider threat include both the malicious/deliberate insider (someone who knowingly causes harm and damage to an organization by stealing, damaging or disclosing information) and the accidental/unintentional insider (a user who is tricked or manipulated into causing harm or whose credentials have been stolen in phishing or other user-focused exploits designed to let attackers pose as legitimate users to access privileged information).
“It’s no surprise that insiders pose the greatest threat to cyber security because they are often the most vulnerable,” Dtex Systems CEO Christy Wyatt says in the company statement.
“As organizations increase perimeter security and lock down their systems, their servers have become more difficult to compromise, but it leaves insiders as the easiest target,” Wyatt cautions. “The need for visibility into user behaviour while keeping employee privacy intact has never been greater,” she contends.
Related: Battle Ready
Other survey findings of concern include the following:
- 68% of enterprises assessed report they believe they have never experienced an insider attack;
- 95% of companies researched say they saw employees researching, installing or using security and vulnerability testing tools;
- 56% of assessments found the potential for corporate data theft by leaving or joining employees;
- 40% of respondents rate malicious insiders as the most damaging threat vector organizations face; and
- 36% of those surveyed rate the accidental or negligent user as most damaging.
“Because organizations typically have a lot more insiders than servers, and it may take only one click on the wrong link or attachment to compromise an organization, adversaries have increasingly focused on insiders as a primary point of attack,” the report states.
Related: Risk management strategies must address “insider threats”: report
Pramod Cherukumilli, head of product management at Dtex Systems, characterizes detecting and managing internal threats as “a Herculean task” for most organizations given the many unknowns associated with the attack vector.
“It’s easier to focus on external threats,” Cherukumilli suggests in the statement.
That said, the report points out it is encouraging that organizations recognize the importance of insider threat.
Still, while results indicate “organizations recognize insider threat as the most potentially damaging component of their threat environments,” the report notes, “there is little indication that most organizations have realigned budgets and staff to coincide with that recognition.”
The report advises that when approaching security, it is important to consider organizational goals or focus on the most important area. The following checklist offers some tips to dealing with the insider threat:
- identify the most critical data within the organization;
- determine who currently has access to data an attacker would target;
- restrict access to information to those who need it;
- get visibility into user behaviour;
- know the threats;
- know the vulnerabilities; and
- identify countermeasures to minimize or reduce the threat.

Have your say: