
Kaspersky finds “invisible” cyberattacks in 40 countries using legitimate software
February 10, 2017 by Canadian Underwriter
Print this page Share
Global cybersecurity company Kaspersky Lab has reported that it has found “invisible” cyberattacks in 40 countries, attacks that are using only legitimate software.
 The series of targeted attacks use “widely available penetration-testing and administration tools, as well as the PowerShell framework for task automation in Windows – dropping no malware files onto the hard drive, but hiding in the memory,” Kaspersky explained in a press release earlier this week. “This combined approach helps to avoid detection by whitelisting technologies, and leaves forensic investigators with almost no artefacts or malware samples to work with. The attackers stay around just long enough to gather information before their traces are wiped from the system on the first reboot.”
The series of targeted attacks use “widely available penetration-testing and administration tools, as well as the PowerShell framework for task automation in Windows – dropping no malware files onto the hard drive, but hiding in the memory,” Kaspersky explained in a press release earlier this week. “This combined approach helps to avoid detection by whitelisting technologies, and leaves forensic investigators with almost no artefacts or malware samples to work with. The attackers stay around just long enough to gather information before their traces are wiped from the system on the first reboot.”
Banks, telecommunications and government organizations in the United States, South America, Europe and Africa were among the top targets. A “small number” of infections were also found in Canada.
Kaspersky said in the release that at the end of 2016, its experts were contacted by banks in the Russian Commonwealth, which found that the penetration-testing software, Meterpreter, “now often used for malicious purposes,” in the memory of their servers when it was not supposed to be there. Investigators discovered that the Meterpreter code was combined with a number of legitimate PowerShell scripts and other utilities. “The combined tools had been adapted into malicious code that could hide in the memory, invisibly collecting the passwords of system administrators so that the attackers could remotely control the victim’s systems,” Kaspersky warned. “The ultimate goal appears to have been access to financial processes.”
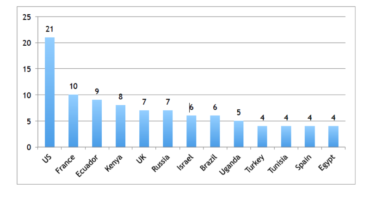
Kaspersky has since uncovered that these attacks are happening on a massive scale, with infections registered in 40 countries. More than 140 enterprise networks were hit in a range of business sectors, with “most victims located in the USA, France, Ecuador, Kenya, the [United Kingdom] and Russia.”
 It is not known who is behind the attacks and the attackers are still active. The use of open source exploit code, common Windows utilities and unknown domains makes it almost impossible to determine the group responsible, or even whether it is a single group or several groups sharing the same tools, Kaspersky said in the release, adding that known groups that have the most similar approaches are GCMAN and Carbanak/a>.
It is not known who is behind the attacks and the attackers are still active. The use of open source exploit code, common Windows utilities and unknown domains makes it almost impossible to determine the group responsible, or even whether it is a single group or several groups sharing the same tools, Kaspersky said in the release, adding that known groups that have the most similar approaches are GCMAN and Carbanak/a>.
“The determination of attackers to hide their activity and make detection and incident response increasingly difficult explains the latest trend of anti-forensic techniques and memory-based malware,” said Sergey Golovanov, principal security researcher at Kaspersky Lab. “That is why memory forensics is becoming critical to the analysis of malware and its functions. In these particular incidents, the attackers used every conceivable anti-forensic technique; demonstrating how no malware files are needed for the successful exfiltration of data from a network, and how the use of legitimate and open source utilities makes attribution almost impossible.”
Have your say: